Hackers Are Posting the Claude Code Leak With Bonus Malware
Summary
Security roundup: the leaked source for Anthropic’s Claude Code has been reposted across GitHub, and some of those reposts include hidden infostealer malware. Anthropic has been issuing takedown notices to remove copies. The piece sits inside a wider briefing covering an FBI surveillance-tool breach now treated as a national-security “major incident”, a huge $280M crypto theft likely linked to North Korean actors, a large software supply-chain compromise that touched Cisco source code, and a recent botnet takedown led by law enforcement.
Key Points
- Anthropic accidentally exposed Claude Code; copies rapidly appeared on GitHub.
- Some reposted repositories were weaponised: attackers embedded infostealer malware into code or installer scripts.
- Anthropic issued copyright takedown notices to remove copies; initial effort targeted thousands of repos then narrowed to dozens.
- Previous tricks exploited Google ads and fake install guides to trick users into running malicious install commands.
- The article is part of a broader security roundup: the FBI declared a major incident after a breach of wiretap tools; Cisco source code was stolen via a Trivy-linked supply-chain compromise; and crypto platform Drift lost $280M in an apparent North Korean-linked heist.
- Law enforcement recently dismantled large botnets (Aisuru, Kimwolf and others) that had infected millions of devices.
Content Summary
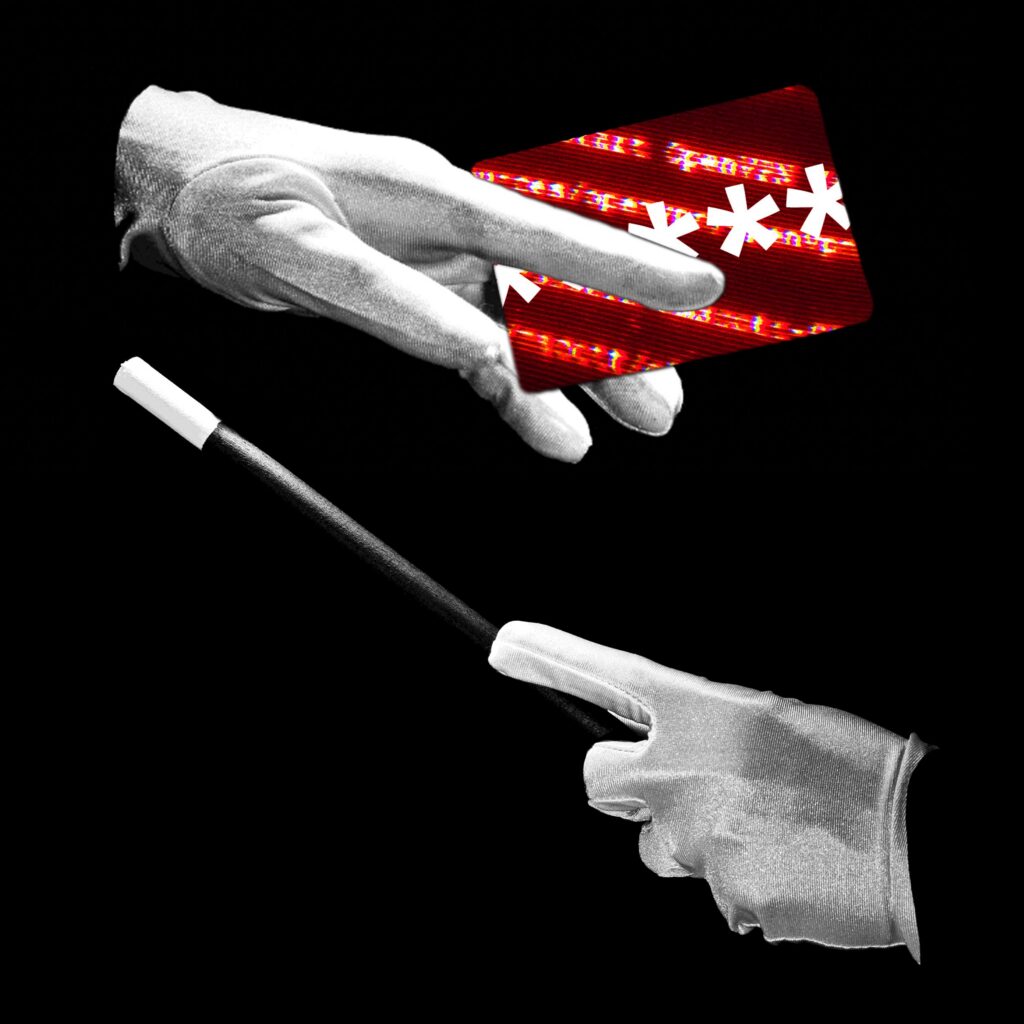
The main story explains how interest in Anthropic’s leaked Claude Code has been weaponised: attackers repost code on GitHub but modify it or its installers to include infostealer malware that exfiltrates credentials and data when users copy-and-paste commands. Anthropic has been issuing takedowns to remove unauthorised copies.
The roundup then highlights several other major security incidents: the FBI treating a recent intrusion into one of its surveillance-collection systems as a major FISMA incident (with China suspected), a record $280M theft from the Drift DeFi platform likely linked to North Korean actors, and TeamPCP-linked supply-chain attacks that led to parts of Cisco’s source code being stolen via a compromised Trivy environment. Finally, it notes a US-led takedown of multiple large botnets that had been used for enormous DDoS campaigns.
Context and Relevance
This story sits at the intersection of AI tooling, open-source distribution and classic malware opportunism. As AI tooling and plugin ecosystems expand, attackers increasingly weaponise the trust users place in GitHub repos and installation scripts. The other items in the roundup underscore that large-scale, state-linked and criminal campaigns continue to exploit supply chains, cloud tooling and decentralised finance to steal data and funds. If you develop, deploy or simply experiment with AI plugins or third-party code, this is directly relevant to your operational security and dev practices.
Author style
Punchy: this isn’t just screencap fodder — it’s a reminder that code availability + user copy-paste behaviour = a low-effort, high-impact attack vector. Read the details if you ship or test code, or manage security for dev teams or CI/CD pipelines.
Why should I read this?
Because if you ever paste install commands or grab plugins from GitHub, you could be installing spyware without realising it. We’ve cut through the noise and flagged the exact ways attackers are hiding nasties in what look like harmless AI code drops — so you don’t have to waste time digging through dozens of repos yourself.