EtherHiding: The trojan in your toolchain – Canadian Centre for Cyber Security
Summary
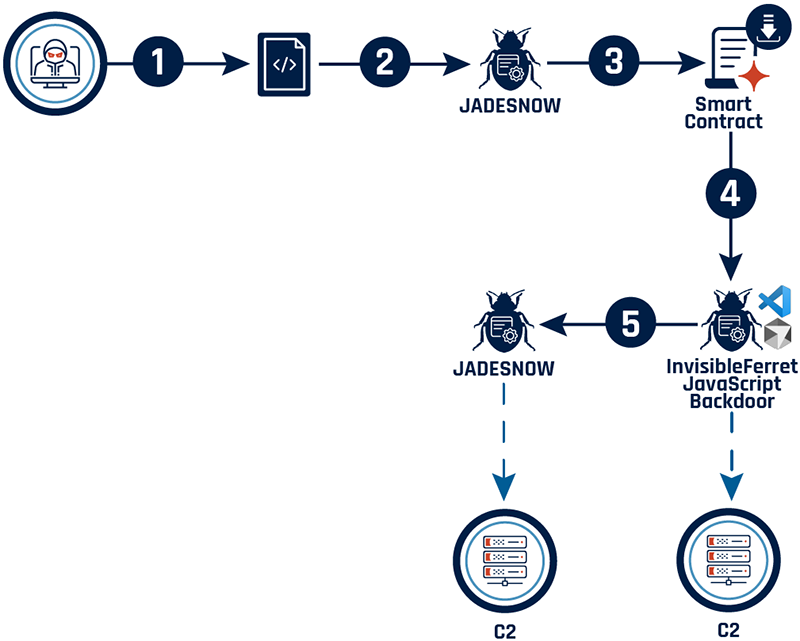
The Canadian Centre for Cyber Security (Cyber Centre) analysed a campaign that uses a technique dubbed “EtherHiding” to hide and deliver malware via blockchain-referenced payloads. In the investigated incident a malicious one-liner JavaScript downloader was inserted into a Tailwind CSS configuration file (tailwind.config.js), padded with extensive whitespace so it blended into developers’ repositories and code reviews.
The hidden loader (jadesnow) fetches transaction hashes from TRON/Aptos, retrieves encrypted payloads from Binance Smart Chain via JSON-RPC, XOR-decrypts them and executes successive downloaders. The final payload is a JavaScript backdoor named InvisibleFerret: it injects into VS Code / Cursor AI internals to persist, generate machine IDs, maintain C2 communication (HTTP POST and socket.io), and exfiltrate files or entire directories.
The Cyber Centre provides detailed TTPs, IoCs (filenames, SHA256 hashes, C2 IPs/URLs and ports), YARA rules for detection, and mitigation recommendations to help organisations and developers detect and respond to this supply-chain targeting of developer tooling.
Key Points
- The initial compromise involved a modified tailwind.config.js containing an obfuscated JavaScript downloader padded with whitespace to evade review.
- Jadesnow downloaders use blockchain transaction hashes (TRON, Aptos) and Binance Smart Chain JSON-RPC to host and retrieve XOR-encrypted payloads.
- The final backdoor, InvisibleFerret.JavaScript, infects VS Code / Cursor AI modules (deviceid) to maintain persistence and track users across sessions.
- InvisibleFerret supports remote commands (file/directory upload, arbitrary JS eval, VS Code injection, discovery and exfiltration) and attempts reconnection every 5 seconds if dropped.
- Exfiltration is implemented with recursive HTTP uploads using Axios and multipart/form-data, enabling theft of source code and entire directory trees.
- Provided IoCs include malicious file names (tailwind.config.js), SHA256 hashes, C2 endpoints (/verify-human/5-74, /u/f/), C2 IPs (166.88.4.2, 23.27.202.27, 23.27.202.143, 136.0.9.8) and port 27017.
- Cyber Centre released a YARA rule to detect the jadesnow obfuscated downloader appended to legitimate projects and used AssemblyLine for large-scale triage.
- Mitigation advice: treat developer workstations and repositories as high-risk, monitor for modified config files, scan for provided IoCs and deploy the YARA detection where possible.
Context and relevance
This attack demonstrates a growing trend: threat actors abusing legitimate decentralised infrastructure (blockchains) to host and hide malware payloads that target developer tooling and supply chains. It highlights that modern supply-chain attacks no longer only target package registries or CI pipelines, but also repository config files and editors. Organisations that rely on Node.js, Tailwind, VS Code or Cursor AI — and anyone storing sensitive code in internal GitHub repos — should treat this as a significant risk to intellectual property and development continuity.
Why should I read this?
Short version: if you write Node.js, use Tailwind or VS Code (or manage dev teams), this is the sort of sneaky supply-chain compromise that will bite you where you least expect it. The attacker hid a downloader in what looks like a harmless config file, used blockchain-hosted blobs to dodge takedowns, and built a persistent backdoor that can steal entire code trees. Read it so you know what to look for and how to block it — saved you the hours of digging through the technical appendix.
Author style
Punchy: This is high-priority for security teams and developers. The write-up combines clear technical detail (attack stages, observed MITRE techniques, commands, IoCs and a YARA rule) with actionable detection and mitigation steps — worth a careful read if you manage development environments or defend developer endpoints.
Source
Source: https://cyber.gc.ca/en/news-events/etherhiding-trojan-your-toolchain