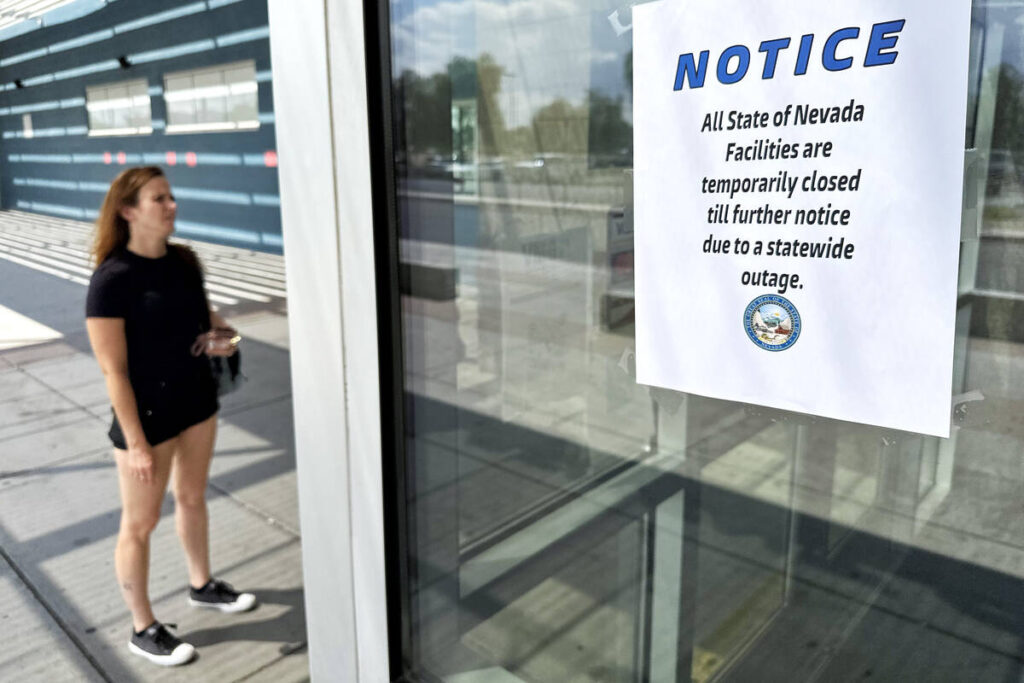
Hackers entered system 3 months before Nevada cyberattack, report says
Summary
Nevada officials released a 30-page after-action report revealing that the threat actor behind the statewide ransomware incident was inside state systems as early as 14 May. The intruder gained initial access when a state employee downloaded a malware-laced system administration tool from a commonly used online resource. Although an anti-malware tool quarantined and deleted the visible malware on 26 June, a hidden backdoor persisted and continued to connect to the attacker’s infrastructure. The attacker later used malvertising (legitimate Google ads) as a delivery vector, moved laterally across networks, accessed critical servers including the password vault, exfiltrated credentials and files, deleted backup volumes and deployed ransomware on 24 August. The state did not pay a ransom, recovered roughly 90% of affected data, and restored services after a 28-day disruption.
Key Points
- The attacker gained initial access on 14 May via a malware-laced system admin tool downloaded by an employee.
- An anti-malware product quarantined and deleted the tool on 26 June, but an underlying backdoor remained active.
- Malvertising (legitimate Google ads) was used to deliver the malware and auto-configure a hidden backdoor that reconnected on user logins.
- Between 16–24 August the intruder accessed multiple critical servers, including the password vault, and retrieved credentials from 26 accounts.
- Investigators found >26,400 files were accessed and 3,241 files were exposed; one exposed document contained personal identifying information of a former employee.
- On 24 August the attacker deleted backup volumes and deployed ransomware, causing 28 days of IT disruption after discovery.
- Nevada declined to pay a ransom, recovered about 90% of affected data, and spent approximately $1.3 million on external vendor response (Mandiant, Microsoft, Dell, Aeris, legal counsel) plus nearly $210,600 in overtime wages (about $259,000 with benefits).
- The Governor’s Technology Office recommends hardening access controls: separate regular and admin accounts, limit privileged access, secure passwords and reduce the number of powerful accounts.
- The full Statewide Cyber Incident After-Action Report is available online for detailed technical and remediation guidance.
Context and relevance
This attack highlights how routine behaviour — downloading a trusted-seeming admin tool and the unintentional reach of malvertising — can give attackers long-term footholds. It underlines growing trends in targeted ransomware operations: persistence through hidden backdoors, abuse of legitimate services for delivery, and focused theft of credentials to move laterally. For public-sector IT teams, auditors and policymakers, the report offers concrete lessons on incident response costs, the value of pre-negotiated response contracts, and why strict privilege management and backup protections are essential.
Why should I read this?
Short version: this was avoidable, and the report shows exactly how. If you run IT, manage access, or care about how public services stay online, skim the key points and the recommendations — saves you digging through 30 pages. It’s a neat case study in how a single download + malvertising + weak privilege separation turns into a state-level outage.